Cyber Security, Detect & Identify
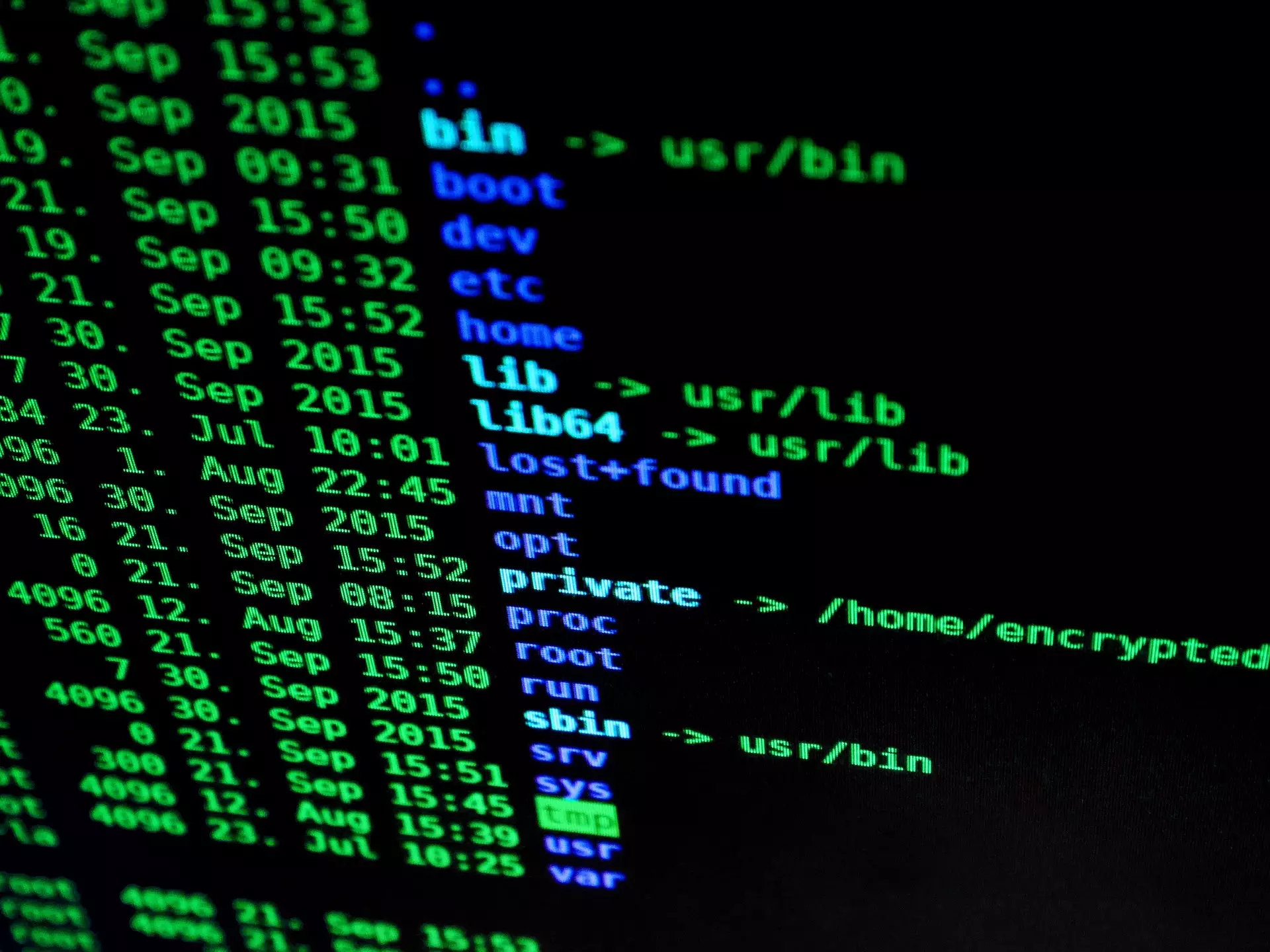
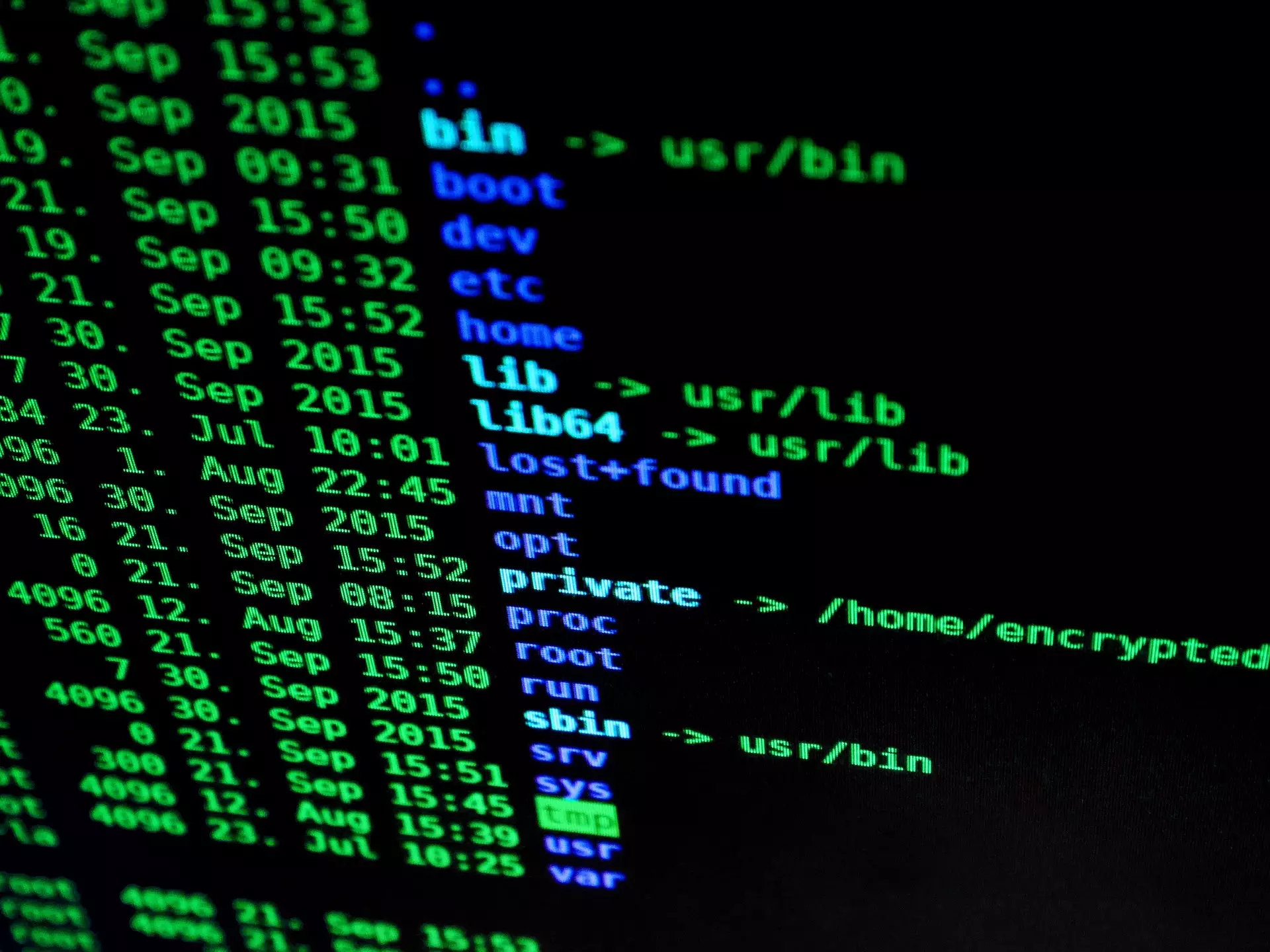
Detect encompasses continuously monitoring systems and networks to identify and detect cyber security events and incidents promptly. It includes activities such as intrusion detection, security information and event management (SIEM), and anomaly detection. Early detection is critical for responding effectively to cyber threats.
Identify, lays the groundwork for the organisation’s cyber security actions moving forward. Determining what exists, what risks are associated with those environments, and how it relates to the business goals of the organisation.
Contents
- News
- Cyber Security - The Six Key Components
- Framework Approach & Methodology
- Cyber Security Challenges & Outcomes - The Consequences of not managing the Six Key Cyber Security Components
- Cyber Security Toolsets for “Identify & Detect”
- TORI Cyber Security Service
- Evidencing Our Experience

